Incident Severity Levels Fully Explained Plus How-To's and Best Practices
When an incident hits, the clock starts immediately. Every minute spent debating how serious it is adds directly to downtime and delays the right response. Incident severity levels solve this by moving the classification decision out of the incident and into the preparation that happened before it.
This guide covers the five standard severity levels and their common notation systems, how incident severity differs from incident priority, how to use an incident severity matrix, and practical steps for defining levels that work for your specific organization.

What Are Incident Severity Levels?
Incident severity levels are a standardized classification system that ranks IT incidents by their impact on business operations, from critical outages affecting all users to minor issues with no functional effect.
They are the foundation of incident triage. The faster a team can classify an incident accurately, the faster the right response begins. In IT Service Management (ITSM) practice, assigning severity correctly is the first step toward restoring normal service operations as quickly as possible.
The numbering works in reverse of what many people expect. A lower number means a more severe incident, and the highest number in your system represents the least disruptive issue.
Most organizations settle on three to five levels. Fewer than three makes it hard to distinguish routine issues from real crises, and more than five introduces classification uncertainty under pressure.
Severity levels do more than label incidents. Each level defines a response chain:
- Who gets notified
- What the target response and resolution times are
- What communication is required throughout the incident
The classification made in the first few minutes sets everything else in motion.
The 5 Incident Severity Levels Explained
The most common framework uses five levels, typically labeled SEV-1 through SEV-5. The definitions below represent standard industry interpretations. Your organization's levels should be set based on your specific business context, user base, and risk profile:
Level |
Name |
P-Equivalent |
Description |
Example |
SEV-1 |
Critical |
P1 |
Complete system outage or major security breach affecting all users or critical infrastructure. Requires immediate, all-hands response. |
Full application outage; confirmed data breach; payment system failure for all customers |
SEV-2 |
High |
P2 |
Significant degradation of core functionality affecting many users. No complete workaround is available. |
Login failures for a large subset of users; critical API unavailable |
SEV-3 |
Medium |
P3 |
Partial functionality loss affecting a limited number of users. A workaround is available. |
Slow API response times; non-critical feature unavailable for some users |
SEV-4 |
Low |
P4 |
Minor issue with minimal user impact. No functional disruption; cosmetic or peripheral only. |
UI misalignment; non-essential alerts misfiring |
SEV-5 |
Informational |
N/A |
No current user impact. Tracked for future improvement. |
Enhancement requests; documentation gaps; minor performance observations |
A Note on SEV-0
Some organizations add a SEV-0 tier above SEV-1 for genuinely catastrophic scenarios. These include complete data loss, ransomware spreading across all systems, or failures that pose a safety risk.
SEV-0 only works as a category if SEV-1 incidents are already rare and clearly defined. If your team is declaring SEV-1 frequently for a wide range of issues, adding SEV-0 just pushes the same problem up one level. The category earns its place when there is a genuine operational need to distinguish between a serious incident and an existential one.
Common Severity Notation Systems
The five-level framework above uses the SEV-X notation common in technology and DevOps organizations. Two other systems are in wide use:
- SEV-X (SEV-1 to SEV-5): Standard in software companies, cloud providers, and teams running on-call rotations. Compact notation that works well in tools, dashboards, and status pages.
- P-X (P1 to P4): Standard in ITSM and ITIL-aligned organizations. Four levels rather than five is typical. P1 is the most severe.
- Plain language (Critical, High, Medium, Low): Preferred by teams that want human-readable labels that communicate meaning without a lookup. Works well when non-technical stakeholders are part of the incident response process.
The notation matters less than consistency. Whatever system your organization adopts, every team should use it the same way, every time.
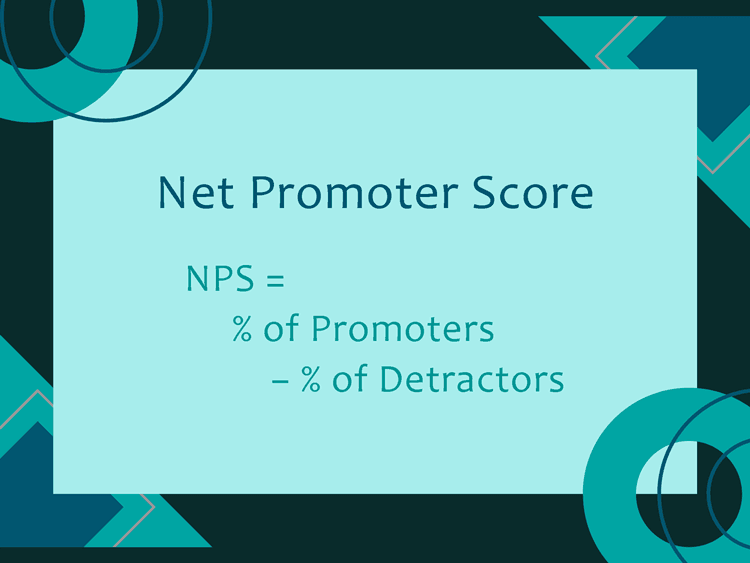
Incident Severity vs. Priority: Understanding the Difference
Severity and priority are related, but they measure different things. Conflating them leads to routing errors, missed Service Level Agreements (SLAs), and frustrated responders.
- Severity measures how much an incident is disrupting users, systems, or business operations right now, based on observable facts.
- Priority measures how quickly the issue needs to be addressed relative to everything else competing for your team's attention.
The two often align. A SEV-1 incident is almost always your highest priority. But they can diverge, and recognizing when they do matters:
- A typo in your company's product name on the public homepage is low severity (no functional impact on users) but might be treated as high priority if it goes live the day before a major industry event.
- A back-end batch processing failure that triggers at 1 AM is technically high severity, but if the first processing window is eight hours away and a workaround is already in place, the urgency is lower than the severity number suggests.
Severity is typically set at incident creation based on observable impact. Priority can shift as business context changes.
Most teams derive priority from a combination of severity and urgency, sometimes using a priority matrix to make that calculation consistent across the team. Routing escalation paths, SLA timers, and on-call notifications off the wrong value produces the wrong results.
The table below summarizes the key differences:
|
Severity |
Priority |
What It Measures |
Impact on users and systems |
Urgency of response |
Who Typically Sets It |
First responder or on-call engineer |
Incident manager or service desk lead |
When It Changes |
Rarely; updated only with new impact information |
Can change as business context evolves |
How It Is Used |
Triggers notifications, SLA timers, escalation paths |
Determines which issue gets worked first |
The Incident Severity Matrix
An incident severity matrix is a grid that maps two inputs against each other to produce a severity classification. Those two inputs are impact and urgency:
- The impact axis measures how broadly and deeply an incident is affecting users or business operations
- The urgency axis measures how quickly the situation will worsen without intervention
The matrix below shows how impact and urgency combine to produce a severity level:
|
High Urgency |
Medium Urgency |
Low Urgency |
High Impact |
SEV-1 |
SEV-2 |
SEV-3 |
Medium Impact |
SEV-2 |
SEV-3 |
SEV-4 |
Low Impact |
SEV-3 |
SEV-4 |
SEV-5 |
To classify an incident using the matrix:
- Assess impact independently: How many users are affected? Is core functionality down or degraded? Is there a security or data risk?
- Assess urgency independently: Is the situation getting worse? How quickly is it spreading? Is a workaround available?
- Find the intersection: High impact and high urgency place the incident at SEV-1. Low impact and low urgency place it at SEV-4 or SEV-5.
- Assign and document: Set the severity in your incident management system and note the reasoning briefly for post-incident review.
The practical value of the matrix is in the process of separating the two inputs before combining them. A classic mistake is letting urgency alone drive classification. For example, an issue that feels urgent because a manager is asking about it every five minutes may still be low severity if few users are affected and a workaround is in place. The matrix keeps those distinctions clear.
The matrix also helps with the inverse case. A medium-impact issue that is spreading rapidly (more users affected every hour) may warrant faster escalation than its current impact suggests. Urgency pulls the classification up even when current impact is still moderate.
Key Factors for Determining Severity
Three factors most reliably predict the correct incident classification for an IT incident:
-
Business Impact
Does the incident halt revenue generation, disrupt critical operations, or threaten business continuity?
A payment processing failure during a peak sales period is a different problem from the same failure at 4 AM on a Tuesday. The business context determines whether impact is genuinely critical or technically significant but operationally manageable.
This is why severity definitions need to be set to your business, not copied directly from a generic framework. An e-commerce company and a healthcare organization may use the same five-level system but draw the SEV-1 line in very different places.
-
Scope of Users
How many users are affected, and which users?
Scope is one of the most straightforward inputs for severity classification. A full outage affecting every customer is a clear SEV-1. A bug affecting a single account is typically SEV-3 or SEV-4. Teams that write their severity definitions in terms of percentage of active users affected find classification faster and more consistent than teams using vague descriptors like "many users."
-
Security Risk
Is sensitive data at risk of exposure or loss?
Security incidents often carry higher severity than their immediate visible impact would suggest. A breach that affects ten users may look like a SEV-3 by scope, but if it exposes personally identifiable information (PII) or signals unauthorized access to production systems, the regulatory and reputational consequences are far more severe. Security risk should be assessed independently and can pull the classification up even when functional impact is limited.
How to Define Incident Severity Levels for Your Organization
-
Start with Business Impact
Before writing any severity definitions, get clear on what "significant impact" means for your specific business. An e-commerce company's SEV-1 centers on revenue loss per minute. A healthcare organization's SEV-1 centers on patient safety and regulatory risk. A SaaS company's SEV-1 centers on service availability and customer trust. The categories don't change, but the thresholds and weights do. Teams that import a generic framework without this calibration step often discover during an actual incident that the definitions don't reflect what their business actually cares about.
-
Set Measurable Thresholds
Vague language is the enemy of consistent classification. "Many users affected" means different things to a startup with 200 customers and an enterprise with 200,000. Replace subjective descriptions with specific, measurable criteria:
- Number or percentage of users affected (for example, "more than 20% of active users cannot access the system")
- Affected revenue rate (for example, "blocking transactions that represent more than $X per hour")
- Specific system or service unavailability (for example, "the authentication system is returning errors for all login attempts")
- Data exposure status (for example, "customer personally identifiable information is confirmed or suspected to be accessible")
PagerDuty's publicly documented severity framework uses this approach explicitly, requiring each severity level to meet specific, team-agreed criteria rather than subjective impact descriptions. The result is classification decisions that can be made and defended in under two minutes.
-
Map Response Times and SLAs
For each severity level, document the target response time and resolution target. The following ranges reflect common industry practice:
Level
Name
Response Time
Resolution Target
Communication
SEV-1
Critical
<= 15 minutes
Continuous until resolved
Hourly updates to management and affected customers
SEV-2
High
<= 30 minutes
4 hours
Updates every 2 hours
SEV-3
Medium
<= 2 hours
Next business day
Status update at resolution
SEV-4
Low
<= 4 hours
Within the week or sprint
Ticket updated at resolution
SEV-5
Informational
Best effort
Future release cycle
No formal communication required
Your actual SLAs depend on customer contracts, regulatory requirements, and what your team can realistically maintain. The table above is a starting point, not a universal standard.
Some organizations also tie severity levels to Service Level Objectives (SLOs), the internal performance targets that SLAs are built on. When an incident threatens a key SLO, it may justify a higher severity classification even if the user impact appears moderate.
-
Define Escalation Paths
Each severity level should specify who gets notified, in what order, and through what channel. For SEV-1, that typically means immediate notification to the on-call engineer, the incident commander, and within a defined window, senior leadership and any affected customers. For SEV-4, it might mean a ticket assigned to the next available team member during business hours.
Establish clear escalation authority as well. The first responder sets the initial severity based on available information. Anyone involved in the incident can escalate the classification if new information warrants it. Only the incident commander should downgrade severity, to prevent premature de-escalation during an active incident.
Whenever severity is changed in either direction, document the reason in the incident record. "Downgraded from SEV-1 to SEV-2: confirmed only a subset of customers affected" takes ten seconds to write and is invaluable in the postmortem.
-
Involve Stakeholders
A technically accurate severity framework fails if business teams and IT teams define "critical" differently. Bring in stakeholders from key functions to review and approve the severity definitions, especially at the highest tiers:
- Operations
- Customer success
- Legal
- Senior leadership
When a SEV-1 is declared at 2 AM and executive notifications go out, every person woken up should have agreed in advance that this classification warranted that response. That agreement only happens when stakeholders were part of setting the thresholds, not just handed a document after the fact.
-
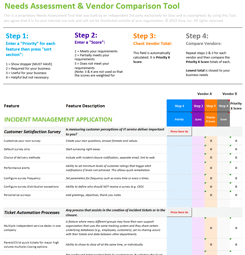
Automate Classification Where Possible
Manual severity assignment under pressure is slower and less consistent than automated assignment based on predefined rules. Modern ITSM platforms with automation and monitoring tools support automated severity classification. An alert that detects full service unavailability can automatically open a SEV-1 incident with the right notifications already triggered.
Automation doesn't eliminate human judgment, and teams can always override an automated classification. What it does eliminate is the "no one remembered to set severity" problem, which is more common than most teams like to admit.
Giva's help desk and ITSM software supports configurable severity rules that connect classification directly to escalation workflows, without manual steps in between.
6 Best Practices for Incident Severity Classification
-
Use 3-5 Severity Levels
Start with the fewest levels that cover your needs. Three to five levels work for most organizations. A six or seven-level system sounds thorough, but under pressure, responders rarely distinguish reliably between that many gradations of impact.
Start with three (Critical, High, Low), add levels when your team genuinely needs the distinction, and stop at five.
-
Prefer Descriptive Labels
Use plain language over code words. "Critical," "High," "Medium," and "Low" communicate meaning immediately. "SEV-1" and "P1" require a mental lookup.
For teams that include non-technical stakeholders in incident response, or that work across departments with different technical backgrounds, plain language reduces the chance that severity gets set incorrectly because someone was unsure what the code meant.
-
Assume Worst Until Proven Otherwise
Classify at the higher level when uncertain. During an active incident, full information is rarely available. Classify at the higher severity, trigger the appropriate response, and downgrade if the situation turns out to be less severe. The cost of over-classifying a single incident is low. The cost of under-classifying a SEV-1 and discovering it 30 minutes later is significantly higher.
-
Eliminate Subjective Language
Write definitions in measurable, objective terms. Review your definitions and flag any phrase that a reasonable person could interpret differently based on context. "Many users affected" is not a threshold. "More than 20% of active users cannot complete login" is. The difference shows up most clearly during a real incident, when there is no time to debate what "many" means.
-
Audit After Every Disputed Classification
Review severity definitions regularly. Set a quarterly review of your severity framework, triggered additionally after any incident where the classification was disputed during response. If your team consistently argues about whether something is SEV-2 or SEV-3, the threshold between those levels needs sharpening. If every incident is SEV-1, the SEV-1 definition is too broad.
-
Post-Incident Review Should Include a Severity Check
Reclassify after the fact. The severity assigned in the first two minutes of an incident is an estimate made under pressure. A Post-Incident Review (PIR), also sometimes called a "postmortem") should check whether the original classification was accurate. Reclassification is not about blame but about having accurate data that feeds root cause analysis and continuous improvement. Incident metrics like Mean Time to Acknowledge (MTTA) and Mean Time to Resolve (MTTR) are only meaningful when sorted against correct severity data.
Common Severity Classification Mistakes to Avoid
Severity inflation is the most common and most costly mistake. When teams default to SEV-1 for every incident that feels serious, the classification loses meaning. Responders begin treating SEV-1 alerts with lower urgency because they have learned that not all of them require an immediate all-hands response. This is alert fatigue. When a genuine SEV-1 arrives, such as a full outage or a data breach, it blends into the noise. Tightening the definition is part of the solution, but it also requires measuring classification patterns regularly to catch drift before it becomes habitual.
Using too many levels creates a parallel problem. Under stress, the difference between a SEV-3 and a SEV-4 is rarely clear enough to be decided in under 30 seconds. If your team is spending more than a moment debating severity during an active incident, you probably have too many levels, definitions that are not specific enough, or both.
Conflating severity and priority in your ticketing system causes routing errors. SLA timers, on-call escalation policies, and stakeholder notification chains are often tied to severity. Priority determines work queue ordering. Using a single field for both means you may escalate incidents that don't need escalation, or fail to escalate ones that do.
Skipping automation leaves classification dependent entirely on whoever picks up the incident first, often a junior engineer under pressure. Even basic automation, such as a monitoring alert for full service unavailability automatically filing a SEV-1 ticket, removes a decision point from a high-stress moment and ensures the right response triggers every time.
FAQs About Incident Severity Levels
-
What is a SEV-1 incident?
A SEV-1 incident is the most severe classification in a standard 1-to-5 framework. It indicates a complete or near-complete system outage with major impact on all users or critical business operations. Common examples include a full application outage, a confirmed data breach, or a payment system failure affecting all transactions.
SEV-1 incidents require immediate response, typically within 15 minutes, and sustained effort until the incident is resolved or contained. The full incident response team is expected to engage.
Stakeholder communication is also a key part of the SEV-1 response. Management and affected customers are notified on a defined schedule, often hourly, for the duration of the incident. A public status page update is common when the outage affects customer-facing systems.
-
What is the difference between severity 1 and severity 2?
The main difference is the scope of impact and the availability of a workaround:
- SEV-1 represents a total or near-total outage affecting the majority of users or a critical business function, with no workaround available
- SEV-2 represents significant degradation or partial outage affecting many users, where core functionality is impaired but not completely unavailable
Executive notifications and public status updates are usually triggered at SEV-1, while SEV-2 may require internal stakeholder updates but not public communication unless the situation escalates.
-
How many incident severity levels should an organization use?
Three to five levels work for most organizations. Three levels (Critical, High, Low) are sufficient for smaller teams or simpler environments where the volume and variety of incidents don't require finer distinctions. Five levels provide more granularity for organizations that handle a high volume and variety of incidents and need to differentiate response expectations precisely.
More than five levels introduce classification uncertainty under pressure and rarely add operational value. If your team finds itself consistently struggling to place incidents in the right tier, the problem is usually in the definitions, not the number of levels. Start simple, and add a level only when the need is demonstrably clear.
-
What is the difference between incident severity and incident priority?
- Severity measures the impact of an incident on users and business operations
- Priority measures urgency, meaning how quickly the issue needs to be addressed
A high-severity incident is almost always treated as high priority, but the relationship is not automatic. A low-severity cosmetic issue might be high priority for brand or contractual reasons, and a high-severity back-end failure with a workaround in place may carry lower urgency than its severity level suggests. Managing both fields separately in your incident management system helps your team make the right call each time.
-
Can a low-severity incident be high priority?
Yes. Severity and priority are separate measurements, and they can diverge in both directions. A low-severity issue with no functional impact on users can be high priority if it affects a visible customer-facing page before a major event, involves a contractual obligation, or creates a regulatory concern.
Conversely, a high-severity incident can carry lower urgency if it occurs off-peak, a workaround is in place, and the business impact is temporarily contained. Teams that keep severity and priority as separate fields in their ticketing system can track each accurately and report on response quality over time.
Related Giva Resources
For more on incident management processes and tools:
- IT Incident Management
- Major Incident Management
- ITIL Incident Management Best Practices
- Incident Resolution Guide
Clear Severity Levels, Faster Incident Resolution
Incident severity levels are one of the most practical frameworks an IT team can put in place. The concept is not complex. Three to five well-defined tiers, each with clear thresholds and a defined response chain, is all most organizations need. The difference between having them and not having them shows up in response time, SLA compliance, and team confidence during a crisis.
The organizations that get the most value from severity frameworks are not the ones with the most levels or the most elaborate definitions. They are the ones where every person involved, from the on-call engineer to the department head, uses the same classifications the same way, every time. That consistency comes from measurable thresholds, stakeholder alignment, and the habit of reviewing classifications after the fact. The framework is the starting point, and the discipline of maintaining it is what makes it work.
See How Giva Supports Incident Severity Classification
When an incident hits, the last thing your team should be doing is debating how to classify it. That delay has a real cost in resolution time, SLA compliance, and the confidence of the people depending on your systems. Giva's Help Desk Software and ITSM Software are built to remove that friction.
With Giva, you can configure custom incident severity levels that map directly to your organization's business impact criteria and Service Level Agreements. Severity assignments automatically trigger the right escalation paths, notify the right stakeholders, and enforce the SLA response times your customers and contracts require.
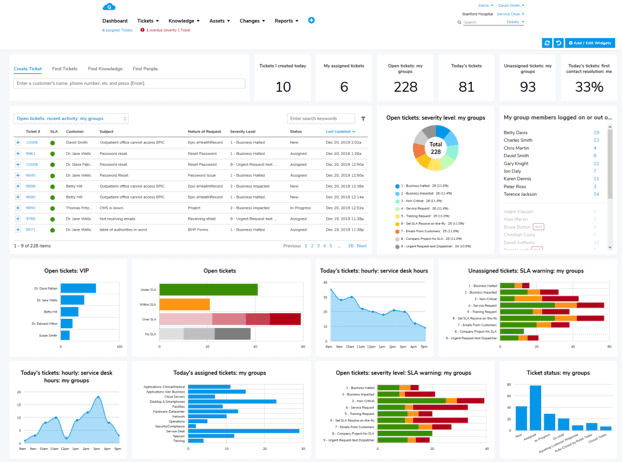
With smart routing, automated notifications, and real-time dashboards, your team stays on top of every open incident, and your stakeholders stay informed.
Beyond incident management, Giva's platform covers the full ITSM picture, including:
Managing incidents at scale requires more than a well-written definitions document. It requires a platform that enforces those definitions consistently, every time. Giva's products give IT teams the tools to classify, escalate, and resolve incidents with confidence.
Get a demo to see Giva's solutions in action, or start your own free, 30-day trial today!