Is This a HIPAA Violation? Take Our HIPAA Quiz
Organizations in the healthcare field will be familiar with HIPAA, formally known as the Health Insurance Portability and Accountability Act. Signed into law in 1996, it sets a national standard for protecting personal health information (PHI). It ensures that patients know how their information is stored and shared through consultation and consent. According to the HIPAA Journal, in the twelve months leading up to October 2023, there were 678 reported data breaches that contained 500 or more records across the country. There is room for improvement in protecting sensitive PHI, especially when dealing with large databases.
HIPAA law violations can result in hefty penalties that range from small fines to jail time for an organization's officers. Whether it be a lack of knowledge on the subject or a blatant disregard for the rules, there are several reasons why organizations across the United States get caught in non-compliance year after year. We could re-iterate the rules, and you can see the HIPAA Compliant section on our website for all things HIPAA, but we thought it might be better to describe what causes a HIPAA violation, and then run through a few common scenarios to help your organization better understand what is compliant and what is not.
What Constitutes a HIPAA Violation?
Simply put, a HIPAA privacy violation occurs when any part of the 115-page document is not adhered to by a healthcare organization. It is the responsibility of each organization to stay up to date with changes to the Act as it evolves to cover new technologies and practices.
There are many ways to violate HIPAA. Some of the most common instances include:
- Not correctly disposing of PHI
- Unauthorized access of PHI by an individual or by providing PHI to those not authorized to access it
- Not providing patients with PHI promptly when they request it
- Not documenting efforts to remain compliant with HIPAA
For more examples, see our HIPAA Common Examples page.
If non-compliant behavior is suspected, it can be reported to the U.S. Department of Health & Human Services (HHS). This government agency also conducts random audits each year, so healthcare organizations should always be ready for a surprise visit by an inspector!
So, what is the best way to prepare? As is required by HIPAA, healthcare organizations and business associates must undergo regular risk analyses. This procedure will identify areas of non-compliance with HIPAA protocols. It is critical to document these analyses and remedy any findings as this documentation may be seized during a random audit or other inspection by the HHS.
What Are the Penalties Associated with HIPAA Law Violations?
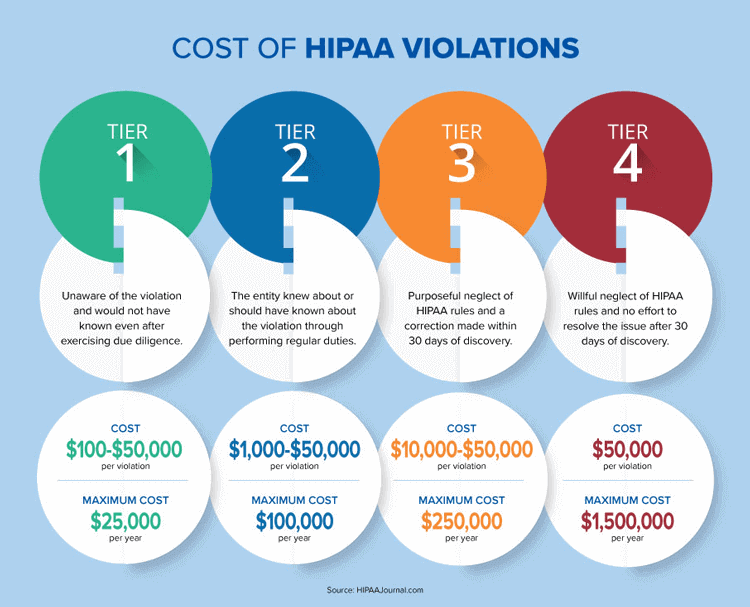
Violating HIPAA rules can come with hefty financial penalties. Unknowingly breaking the rules can result in fines up to USD 50,000, while a willful disregard for the parameters can result in penalties totaling up to USD 1.5 million, per incident, per calendar year. Refer to the infographic below for more details on each tiered category.
Besides financial penalties, breaking HIPAA rules, whether intentional or not, means that individuals' PHI was mishandled. Depending on the severity of the mismanagement, personal information like social security numbers, payment methods, and healthcare conditions could be sold on black markets around the world. Not only does this create stress and anxiety for patients, but it can also be cause for irreparable reputation damage to a healthcare organization. There are many reasons why a healthcare organization should do everything in its power to protect PHI and follow the guidelines set out by HIPAA.
Take the HIPAA Quiz for Employees! Is this a HIPAA Violation, Answers True or False?
-
Scenario 1: "Gossip"
Q: You decide to walk to the reception area to chat with the secretary before your next patient arrives. You begin to discuss the previous patient's specific condition. Knowing that the information is sensitive, you make sure to whisper, doing your best not to be heard by others in the waiting room. Is this form of "gossip" a HIPAA violation?
A: True. Under HIPAA guidelines, PHI cannot be shared with others unless consent is given by the patient. And yes, "others" can refer to employees who work at the same practice. Just because they work there does not mean they are privy to all information available. Sure, maybe nobody heard, and it will not matter, but if someone in proximity hears the conversation, it can be reported to the HHS.
-
Scenario 2: Destroying PHI
Q: To declutter space at your healthcare practice, you decide to discard paper PHI records into the recycling bin. No effort is made to cut up or shred the documents as you figure they will be destroyed once they are picked up by local sanitation workers. Is this form of disposal acceptable under HIPAA guidelines?
A: False. Although HIPAA rules do not mandate exact methods for disposal, they do recommend, "shredding, burning, pulping, or pulverizing the records so that PHI is rendered essentially unreadable, indecipherable, and otherwise cannot be reconstructed." TOTALHIPAA reminds us that healthcare practices should "maintain required documentation for a minimum of six (6) years from the date of its creation, or the date when it last was in effect, whichever is later." So when the time comes to destroy PHI, consider using a provider that offers a cross-cut shredding method for best results. See our HIPAA Basics page for more on medical record destruction.
-
Scenario 3: Stolen Devices
Q: During a company-wide meeting, a thief accesses the premises through an unguarded entrance and steals a few laptops before escaping. This individual accesses data on the devices and shares it on a medical black market in exchange for a hefty crypto payment. Employees return to their desks shocked and confused at what had happened. Who could have predicted a robbery? This certainly cannot be a HIPAA violation could it be?
A: True. This answer may surprise you, but as a healthcare provider and/or practice, it is your duty to protect PHI at all costs, that includes the safety and security of devices that are on and off-site. In this case, it could have been as simple as locking away sensitive tech while away from desk space. It could also include better securing all access points to a facility, including rooftop hatches.
Consider the case of Lahey Hospital and Medical Center in Massachusetts that paid USD 850,000 in relation to sub-par device security standards which led to the loss of data on 599 patients. According to the events recounted through the Digital Guardian, "Lahey notified HHS's Office of Civil Rights in August that a laptop was stolen from an unlocked treatment room in the organization's Burlington, Massachusetts facility. It was on a stand that accompanied a portable CT scanner, operating the scanner and producing images for viewing. At the time the laptop was stolen, it contained the protected health information (PHI) of 599 patients." See our HIPAA-Compliant Devices page for more information.
-
Scenario 4: Using PHI for Educational Purposes
Q: A healthcare provider is invited to participate in a guest-guided class at a local university. The provider decides to bring a few patient X-rays to show the students as examples. Would this be considered a HIPAA violation?
A: False. In fact, PHI can be used in these circumstances without patient authorization (when used for healthcare operations). However, it must be done with safeguards in place. Information like name, date of birth and any other identifying information should be removed. Providers should also be careful not to leave these documents "out in the open." The risks go beyond stolen paperwork, but can also involve students snapping pictures of PHI with their smartphones or other mobile devices.
The Bottom Line: Keep a Vigilant Watch Out for HIPAA Privacy Violations
PHI is as sensitive as it gets. If you have not asked the patient permission to share the data with anyone else, there is a good chance that doing so might be a HIPAA violation. So, play it safe and always ask them or their authorized caregiver first. Remember, HIPAA violations go beyond sending or talking about PHI to unauthorized individuals. Securing your tech devices and properly disposing of old PHI are also important things to consider.
Another way to play it safe is by investing in the right cloud tech to ensure that you can remain focused on caring for your patients while leaving the security and compliance aspect of things to the pros. Consider Giva, providing clients with HIPAA-compliant cloud help desk software for electronic health and medical records. Find out more and sign up for a 30-day, risk-free trial today.