Protected Health Information: Its Significance in HIPAA Compliance (with PHI Examples)
Understanding the intricacies of healthcare data and its protection is crucial in today's digital age. Among the most critical concepts in the realm of healthcare compliance is personal health information or anything that is personally identifiable information such as a person's name or phone number. When linked to health data, they can reveal sensitive information about an individual.
While many might recognize the standard list of 18 HIPAA identifiers, the true depth of PHI's significance lies not just in understanding these examples but in the comprehensive context surrounding them. Within the first half of 2023 alone, 40 million Americans were impacted by 308 reported healthcare data breaches, as noted in Critical Insight's 2023 Healthcare Breach Report, via Bluefin. This is a considerable figure especially when compared to 2021, which saw 58 million people affected by data breaches throughout the entire year. Violations like these emphasize the importance of proper data handling. This post delves into these crucial identifiers and the overarching importance they hold in HIPAA compliance.
What is PHI?
Protected Health Information (PHI) encompasses any health-related information that relates to an individual's health status, healthcare provisions, or payment details and can be used to identify them. Examples of PHI include details like a person's name, medical history, billing information, or insurance information. PHI holds immense significance in the healthcare domain because it contains private information about a person's health journey. Unauthorized disclosure or mishandling of PHI can lead to identity theft, stigmatization, legal repercussions, and irreparable damage to a healthcare organization's reputation. This makes the HIPAA Privacy and Security Rules so vital.
What is PHI under HIPAA?
The Health Insurance Portability and Accountability Act (HIPAA) transformed U.S. Health Information Technology privacy since its introduction in 1996. So, what is HIPAA PHI? Under HIPAA, PHI is any data related to health, healthcare provision, or payment that identifies an individual. HIPAA does not just set storage and access rules; it fosters a culture of confidentiality, mandates regular audits, enforces the HIPAA Breach Notification Rule, and establishes a benchmark in healthcare data protection.
18 PHI Identifiers
Below are 18 specific PHI identifiers that, when associated with health-related data, classify the information as PHI. Here's a breakdown of each:
- Names: This is straightforward and includes full names, last names, maiden names, or any other identifying names.
- Geographical Identifiers: Information regarding an individual's location, excluding the first three digits of a ZIP code, unless it's a geographic unit with 20,000 or fewer people.
- Dates: Any date related to an individual except year--birthdays, admission dates, discharge dates, death dates, etc.
- Phone Numbers: Any personal phone number, whether it's home, work, or cell.
- Fax Numbers: Personal fax numbers.
- Email Addresses: Personal email addresses which can be used to identify an individual.
- Social Security Numbers: A unique number assigned to individuals for various governmental purposes.
- Medical Record Numbers: Unique numbers assigned to individuals' health records by healthcare providers or institutions.
- Health Insurance Beneficiary Numbers: Specific numbers given to individuals receiving health insurance benefits.
- Account Numbers: Numbers related to an individual's account, often seen in healthcare billing and other financial transactions.
- Certificate/License Numbers: Numbers on any personal certificates or licenses.
- Vehicle Identifiers: This includes serial numbers, license plate numbers, or any other identifier related to personal transportation.
- Device Identifiers and Serial Numbers: Numbers related to any personal medical devices.
- Web URLs: Personal web addresses or IP addresses.
- Biometric Identifiers: This includes fingerprints, retina scans, voice prints, and DNA.
- Full Face Photos and Comparable Images: Any photograph or image that can be used to identify an individual.
- Any other Unique Identifying Number, Characteristic, or Code: This is a catch-all for any other unique identifier not specifically listed.
- Age: Especially if over 89. Specific ages and elements may be aggregated into a single category of age 90 and older to maintain anonymity.
Each of these identifiers is significant because, when linked with health-related data, it can reveal sensitive and private information about an individual.
What is Not PHI?
While understanding what constitutes PHI is vital, it's equally important to recognize what doesn't fall under this category. Just because information pertains to health doesn't automatically classify it as PHI under HIPAA regulations. Here are a few examples of items which may not be considered PHI:
- De-identified Information: Data from which all 18 HIPAA identifiers have been removed is not PHI. For instance, a database containing only medical conditions without names, addresses, or any other personal identifiers is not considered PHI.
- Health Information Not Handled by HIPAA-Covered Entities: Information you search for or share about health conditions on public forums, websites, or apps that aren't connected with health plans, healthcare professionals or providers, or healthcare clearinghouses is not PHI.
- Employment Records: Health data that an employer obtains about an employee (like sick leaves or physical exam results) and that isn't maintained by a healthcare provider or used to make decisions about healthcare treatments or payments is not deemed PHI.
- Education Records: Health information maintained by educational institutions under the Family Educational Rights and Privacy Act (FERPA) is not PHI. For example, a school's record of students' vaccinations is not PHI unless shared with a healthcare provider for treatment purposes.
- Data Used for Non-Health-Related Purposes: Information collected for a reason unrelated to healthcare, like a fitness tracker simply monitoring your steps without linking it to any health outcome or recommendation, doesn't fall under PHI.
PHI Examples vs Non-PHI Scenarios Side by Side
-
PHI Example: A medical record noting that John Doe was treated for a fractured arm on a specific date.
Not PHI: A general article on the internet discussing the treatment and recovery process for fractured arms.
-
PHI Example: An email from a doctor to a patient, Jane Smith, discussing her recent blood test results.
Not PHI: A generic post on a health forum discussing normal blood test value ranges.
-
PHI Example: A billing statement for Mike's recent surgery.
Not PHI: A general price list of surgeries available on a hospital's website.
Understanding the boundary between what is and isn't PHI is crucial for proper data handling, ensuring patient privacy, and adhering to HIPAA regulations.
How to Be Secure Under PHI
In the rapidly evolving digital realm of healthcare, ensuring the security of Electronic Protected Health Information (ePHI) isn't just a best practice — it's a regulatory mandate. But when we ask, "What is HIPAA PHI?", we're diving into a stringent set of Security Rules specifically designed to safeguard sensitive patient data. As healthcare systems become increasingly reliant on software and IT infrastructure, the measures taken to protect this data must be equally advanced.
-
Encryption
Encryption stands as a frontline defense in PHI security. By converting data into a code to thwart unauthorized access, encryption ensures that, even if breached, the data remains unreadable. This is vital for electronic PHI (ePHI), demanding that contemporary healthcare software utilizes top-tier encryption both when data is in transit and when stored.
-
Access Control
It's essential to remember that within a healthcare organization, not every individual should access all patient data. Implementing access controls, like user authentication and specific authorization systems, ensures PHI is accessed only by those who genuinely require it. Role-based permissions and multi-factor authentication further bolster PHI's security.
-
Regular Audits
Regular audits serve as preventative check-ups for an organization's data security health. By consistently examining system logs and access patterns, potential vulnerabilities or irregularities can be pinpointed and addressed, reinforcing the integrity of PHI.
-
Employee Training
A critical component in understanding "What is HIPAA PHI?" revolves around ensuring all staff are well-versed in its intricacies. Human errors, often due to lack of knowledge, can lead to significant breaches. Periodic training, threat updates, and breach simulations empower employees to handle PHI judiciously.
-
Incident Response Plans
Despite the most rigorous measures, breaches can still occur. Having a comprehensive incident response plan ensures that, if a breach is detected, the steps to mitigate its effects are clearly defined. From identifying the breach's scope to communicating with affected parties, a structured plan reduces potential damages.
The Bottom Line: Embracing Responsibility in PHI Protection and Compliance
When we ask "what is PHI?", we're diving into the vast world of healthcare data. While knowing the critical identifiers is a start, it's the protection of this data that truly matters.
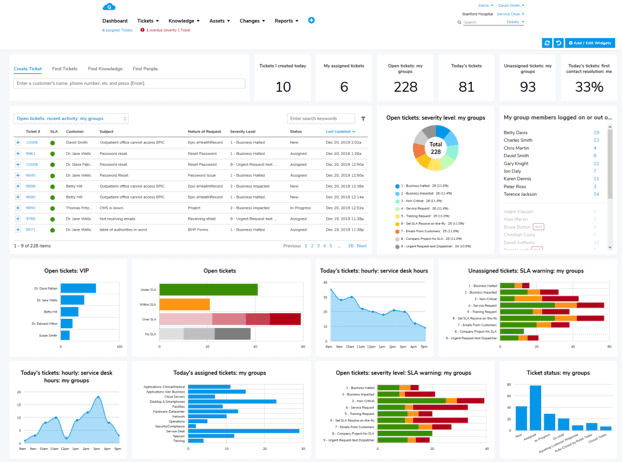
HIPAA violations can lead to hefty fines, among other repercussions, so tools like Giva Customer Service software in the cloud becomes vital. With its HIPAA-compliant setup, Multi-factor Authentication, and a full suite of helpful modules, it offers healthcare organizations a robust solution for managing and protecting patient data. If you're keen to step up your data protection game, consider taking advantage of a 30-day free trial. Properly safeguarding PHI isn't just a goal — it's a responsibility.