HIPAA vs HITRUST vs HITECH: What's the Difference?
When it comes to Protected Health Information (PHI), healthcare providers and organizations can never be too safe. The repercussions for lost, stolen or manipulated data could cost you large sums of money, a tarnished reputation, and even jail time. According to data shared by HIPAA Journal, there were 339 healthcare data breaches of 500 or more records reported to the Department of Health and Human Services' Office for Civil Rights (OCR) Between January 1, 2023, and June 30, 2023.
Although following the strict guidelines of HIPAA can save you plenty of potential trouble, you may also consider HITECH and HITRUST as supplemental forms of security assurance. How do they relate to each other and work together? Let us find out.
What is HIPAA?
The Health Insurance Portability and Accountability Act of 1996, shortened to HIPAA, is a United States Act of Congress enacted and signed into law on August 21, 1996. It is a national standard of guidelines used by healthcare organizations to protect Protected Health Information (PHI), especially in instances where there is no patient knowledge or consent. Cyberattacks and internal bad actors are such examples of situations where PHI can be compromised. These sensitive data sets are valuable to bad actors because they can be sold in online black markets. They can also be used as "bait" when looking to extort organizations for money (think ransomware). The prospect of financial penalties, damaged reputations, and even jail time for corporate officers makes protecting PHI or re-acquiring it after a loss the utmost priority. Following the guidelines of HIPAA and retaining logs of your efforts can provide peace of mind and help you pass random audits.
Learn more about HIPAA Basics: Understanding the Health Insurance Portability and Accountability Act of 1996
What is HITRUST®?
The Health Information Trust Alliance (HITRUST) Common Security Framework assists healthcare organizations and third parties in achieving compliance with HIPAA regulations. Based in Frisco Texas, it provides its clients with a step-by-step process toward "HITRUST Certification." The certification will take an organization and its members through modules aimed at growing information security and cybersecurity maturity levels. The program itself is tailored to the scope and size of your organization. With that said, it is still most likely used by larger healthcare organizations and their business associates. Small to medium-sized organizations, which often have fewer employees and a more manageable amount of data, may find the investments involved in certification time and cost prohibitive.
HIPAA vs. HITRUST
To put things into layman's terms, If HIPAA is the "what," then HITRUST would be the "how." The U.S. Department of Health & Human Services (HHS) and the Office for Civil Rights (OCR) conduct audits for HIPAA and National Institute of Standards and Technology (NIST) Cybersecurity Framework protocols, meaning HITRUST certification is not federally mandated, though many compliance controls required by HIPAA or HITECH are covered by its framework, including ISO, NIST, and PCI.
What is HITECH?
The HITECH Act of 2009, (HITECH stands for the Health Information Technology for Economic and Clinical Health Act), is a component of the American Recovery and Reinvestment Act (ARRA). This economic stimulus package was brought in by the United States government following the recession of 2008 to promote recovery. This was done by creating jobs, improving infrastructure, and stabilizing budgets across all levels of government.
HITECH was built into ARRA to encourage technological advances in both the healthcare and science fields. What is HITECH in healthcare? It depends on what part of the system you occupy. For HIPAA Covered Entities, HITECH pushed the uptake of Electronic Health Records (EHRs), moving away from pen-and-paper data recording and storage. For Business Associates, HITECH insisted on compliance with the HIPAA Security Rule whenever working with a patient's PHI. Patients received the benefit of a healthcare system that was more secure and innovative.
HIPAA vs. HITECH?
When it comes to PHI security, we hear almost exclusively of HIPAA. It provides adequate guidance to protect sensitive data and avoid penalties. However, If you have made it this far into the article, you might be wondering — what is the difference between HIPAA and HITECH? Well, not much! HITECH has played a critical role in shaping recent amendments to HIPAA. This point is especially true as it relates to privacy and security rules, Business Associate compliance with these rules, and the introduction of the Breach Notification Rule. Let us dive into more detail:
-
Business Associate Accountability
The HITECH Act requires that Business Associates of healthcare organizations or any HIPAA Covered Entity enter into a BAA, or Business Associate Agreement. This requirement serves a couple of important purposes. First, the Business Associate must not share PHI unless authorized under the HIPAA Privacy Rule. The Business Associate is also compelled to take all necessary measures to protect privacy, integrity, and availability of PHI, not limited to documenting these efforts in the case of an audit.
The HITECH Act also brought forward the need for subcontractors of business associates to enter into a BAA.
-
Greater Penalties
Before HITECH, when a Business Associate caused an infraction, they were directly fined. HITECH Compliance increased the legal liability of both the Business Associate and the HIPAA Covered Entity. They each can receive fines when the infraction originates at the Business Associate level.
The HITECH Act also amended the penalty structure of violations to include when it is without a Covered Entity's knowledge. Despite this, the Covered Entity or Business Associate should have taken precautions to avoid the type of breach in the first place.
-
Improved Patient Access
With new technology comes greater efficiency and control. Today's healthcare patients have unparalleled control over their PHI. This is primarily due to the HIPAA Privacy Rule and its extended reach under HITECH. Patients now have the right to obtain electronic copies of their PHI at their request, and they must be received in specific timeframes.
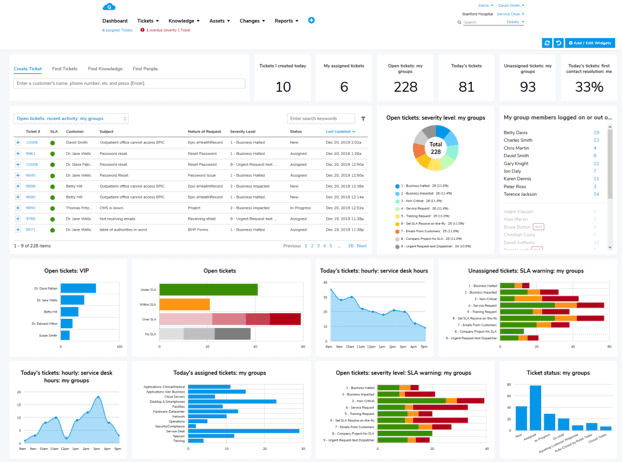
Check it out: Giva's Certificates of Compliance & Security
The Bottom Line: Compliance Requirements Go Beyond HIPAA
- HIPAA is the "what"
- HITRUST is the "how"
- HITECH is HIPAA's "bodyguard", helping to protect and further refine existing HIPAA policies
The onset of tech in healthcare is certainly beneficial and efficient, although it can create more avenues for PHI to be compromised. Always safeguard PHI — need a reminder of fines associated with HIPAA non-compliance?
Penalty Tier |
Level of Culpability |
Minimum Penalty per Violation Type |
Maximum Penalty per Violation Type |
Annual Penalty Limit |
Tier 1 |
Lack of Knowledge |
$137 |
$34,464 |
$34,464 |
Tier 2 |
Lack of Oversight |
$1,379 |
$68,928 |
$137,886 |
Tier 3 |
Willful Neglect |
$13,785 |
$68,928 |
$344,638 |
Tier 4 |
Willful Neglect not Corrected within 30 days |
$68,928 |
$68,928 |
$2,067,813 |
Covered entities, such as healthcare organizations, should keep in mind that the protection of PHI does not stop at HIPAA. HITRUST and HITECH are critical components which can paint a larger picture. HITRUST can ensure you are well educated and certified on requirements, while HITECH has formed some of the most important building blocks to HIPAA as we know it today.